 Linux Networking |
 Linux Networking |
Networks can be thought of as consisting of end points and transfer points. The end points are where the work is done, while the transfer points cause communications to function. Of course in reality things are not quite this simple, but for the most part the model is pretty good. Routers, gateways, and so forth as the transfer points, while workstations and servers are the end points.
Up until this point, we have discussed issues primarily related to the functioning of end point, but now it is time to move on to transfer points. Each transfer point can be characterized as having some number of interfaces (we sometimes use the term 'face' instead of interface), each covering some set of address ranges. Between these faces, routes dictate how traffic that is transferred by the transfer point gets transferred. In addition, these faces may act to masquerade the address spaces associated with other faces so that appearances on one face as to IP addresses and ports are not the actual addresses and ports that appear on the other face.
Each interface can also allow, deny, or alter IP addresses, ports, flags, fields, and content based on direction of transfer, context, content, addresses, ports, flags, and fields. In the firewalls course that follows this one, details of access controls will be discussed further, but for now we will be predominantly concerned with addresses, routes, masquerades, and IP address filtering, all of which are fundamental to the proper functioning of a network.
Assigning addresses to each interface and the network it is to support requires a network architecture of some sort. Once the overall design of the network is done, getting traffic to flow starts with configuring the addresses, network masks, and broadcast addresses of each face of the system. For example, if we are routing between three networks, we need to configure three network interfaces, one for each network.
Each network interface will have an IP address on the network it interfaces to, typically with the next to the top or bottom address of the network. So for a class C network (255 addresses - the whole last byte of an IP address) , you would expect the gateway computer to be at a.b.c.254 or a.b.c.1. This is a convention only and need not be followed, however, the '.0' and '.255' address are to be avoided because they have a tendency to create faults in systems due to the use of the .255 address for broadcast packets and the '.0' address for masking out portions of networks. For this example, we will use the following addresses:
| Face | IP address | Netmask | Broadcast |
|---|---|---|---|
| eth0 | 10.0.0.1 | 255.255.255.0 | 10.0.0.255 |
| eth1 | 192.168.0.1 | 255.255.0.0 | 192.168.255.255 |
| eth2 | 204.7.229.1 | 255.255.255.0 | 204.7.229.255 |
We then use ifconfig as follows:
wg:root /root> ifconfig eth0 10.0.0.1 netmask 255.255.255.0 broadcast 10.0.0.255
wg:root /root> ifconfig eth1 192.168.0.1 netmask 255.255.0.0 broadcast 192.168.255.255
wg:root /root> ifconfig eth2 204.7.229.1 netmask 255.255.255.0 broadcast 204.7.229.255
Next we have to define routes for traffic flow. In a static routing situation we normally provide routes based on known bandwidth to known locations and use a default route for all of the rest of the traffic. For example, in a corporate network we might have several class C networks behind a router in another city. We would want all internal traffic between the two cities to flow across a leased line between cities, but within each city we might want external traffic to flow through our ISP to the Internet.
In this case we will assume that the default Internet gateway computer is 204.7.229.254 (the way we reach the Internet from here) and that we have two leased lines to other parts of our internal network, each with several IP address ranges:
wg:root /root> route add default gw 204.7.229.254 eth0
wg:root /root> route add -net 12.12.13.0/24 gw 192.168.0.254 eth1
wg:root /root> route add -net 12.251.193.0/24 gw 192.168.0.254 eth1
wg:root /root> route add -net 172.25.92.0/24 gw 192.168.0.254 eth1
wg:root /root> route add -net 203.5.0.0/16 gw 204.7.229.254 eth2
wg:root /root> route add -net 108.23.25.0/24 gw 204.7.229.254 eth2
wg:root /root> route add -net 112.221.9.0/24 gw 204.7.229.254 eth2
The '/24' and '/16' notation indicates the network masked off by 24 or 16 'on' bits respectively. In other words, 172.25.92.0/24 covers IP addresses 172.25.92.0-172.25.92.255 while 203.5.0.0/16 covers 203.5.0.0-203.5.255.255. In this way we have specified that traffic that appears in this system destined for any of the addresses specified for eth2 will get sent out that interface. Note that with static routing such as this, if the link between here and the computer at the other side of eth1 or eth2 fails, no alternative routing will be attempted for these packets in this system and it is likely that the communication will fail until that link is restored.
In Linux systems, there is often a requirement to enable forwarding of packets between interfaces in order for the computer to properly act as a router. This is done on the White Glove and most other current systems through the use of the '/proc' file system. The typical command is:
wg:root /root> echo 1 > /proc/sys/net/ipv4/ip_forward
This directory includes a wide range of other 'files' that correspond to variables in the kernel that dictate how traffic will be managed. Some of them are listed here:
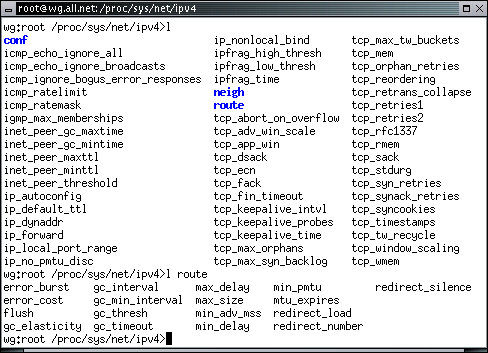
Typically, echo'ing a 1 to the file enables and echo'ing a 0 disables the function. For example, to ignore all ICMP echo packets (pings), you would echo a 1 to icmp_echo_ignore_all.
One of the nice features of Linux is that it provides for the ability to masquerade an entire network behind a single IP address. This is particularly handy for the most common gateways between ISPs and home or small business networks. In this case, we will assume that the Internet is on one face and the internal network is on the other face. The objective is to allow those inside the network to browse the Internet with all of them appearing to come from the same IP address. Of course inbound traffic can only be properly directed if the traffic originated from inside the masquerade or if a special filter is created to manage this.
Masquerading is normally a firewall function, but we will provide this one example, both to wet your appetite for the Linux firewalls course and to provide you with the means to get your local network up with only a single external IP address.
One of the nicest features of the White Glove CD is its utility as an automatically initialized and customized system with only read-only media. This feature allows you to configure a routing device, such as the one above, or a server or other fixed function networked system, and have it automatically restore itself to the proper configuration at restart. This often happens in the case of a power outage, but it's also handy for a gateway that you shut off at the end of the day and start back up in the morning. Because all of the data required to run the system will be stored on a floppy disk and the bootable CD, none of it can be altered by any non-physical attack on the system. In the worst case, all you have to do to restore the system is turn the power off and back on again.
This feature is particularly handy for a routing device because there is very little information that has to be stored, so it easily fits on a floppy disk. It is also very handy when computer hardware breaks because the complete reconfiguration process consists of replacing the hardware with another computer that has the right number of interfaces, rebooting with the original CD and floppy, and plugging the network cables into the proper interfaces.
| To identify the proper interface for each network, boot under White Glove without the floppy present and use 'tcpdump' to view each Ethernet one at a time (using the '-i ethX' option where X is replaced by the desired Ethernet number). Plug in a cable to one interface, sniff the traffic on interface after interface until you see traffic, and mark the interface with its proper Ethernet number. |
When the White Glove boots, it looks at the floppy disk drive (A: under Windows) to see if there is a recognizable file system. If there is, it is mounted as '/mnt/floppy'. Next it looks on that file system to see if there is a file called '/mnt/floppy/PLAC.go' or '/mnt/floppy/WG.go'. If such a file exists, it is executed as a shell script before allowing user login to the system. If PLAC.go does not terminate or start up an input process, no further input will be taken (except that [CTRL-ALT-DEL] can be used from the console to reboot the system).
Therefore, in order to get the above router configuration to automatically configure whenever the system is rebooted:
Create a Floppy Disk: This is typically done with the mkfs command which makes a file system. Place a write enabled floppy disk in the floppy disk drive that Windows sees as drive A and type the following command (note that this will destroy any previous data on that floppy disk):
wg:root /root> mkfs /dev/fd0
Mount its File System: To make the contents of the floppy disk file system available for use, you must mount it as a file system under Linux:
wg:root /root> mount /dev/fd0 /mnt/floppy
Add Desired Commands to PLAC.go: Using an editor of your choice, create a file called '/mnt/floppy/PLAC.go' which contains all of the commands you want to have executed, in the proper order. For the example above, you would use all of the commands above and any others you wish to add. If you want to provide services as well, start those services with commands in PLAC.go as well.
Unmount the File System: Unmount the floppy disk file system to make certain that it has the necessary data and that all of the information you have asked to be written has actually been written. Please don't remove the floppy while the light on the floppy drive is lit as this may result in incomplete output and a corrupted file system.
wg:root /root> umount /mnt/floppy
Press Reset: Press the reset button on the computer to start it up. Unless you have something else operating on your computer, this will have no negative effect on the system since it has no permanent storage other than the CD-ROM and floppy.
Test: Test this and verify that everything works as it should. If something doesn't work, figure out what to change in the PLAC.go file by stepping through every command manually. find the difference between what it does and what it should do and fix it by going back to "Mount its File System".
Write Protect: Once the floppy does the right thing, set the physical write protect tab on the floppy disk so that both holes in the floppy are showing (i.e., it is write protected) and place it back in the floppy disk drive. This will prevent alteration of the configuration unless and until the floppy is again removed
Your system is ready to go. It can be rebooted at any time and within a minute or two it will be back into it's normal preconfigured operation.
For systems with wireless interfaces, White Glove uses a command called 'wlan'. To view this command and what it does, type:
wg:root /root> cat `which wlan`
Note that this command uses 'back-quotes', quotes that go from upper left toward lower right, not the normal apostrophe character or the double quote. wlan takes optional arguments in the following order; (1) the interface - typically something like 'wlan0', (2) the IP address of the face, (3) the "ESSID" which is a name used by your wireless network to identify itself to itself, (4) the channel number (an integer between 1 and 11 identifying the frequency for communications), (5) the mode which is either 'managed' for networks with wireless hubs or 'ad-hoc' for point to point wireless connections, and (6) the gateway computer for routing purposes. These are all defaulted to a setting that it almost certainly wrong for your wireless LAN.
Once this is properly configured, your wireless LAN should operate just as any wired LAN works from a standpoint of routing and gateway behavior.
We have covered a model for how network transfer points work, how to assign addresses to interfaces, how to add static routes to interfaces for direction of traffic, how to do IP Masquerading, how to configure a floppy disk for automatic network transfer point startup and restart, and how to apply these things to wireless. By now you should be ready to start configuring network transfer points for substantial Linux networks.